The ACM Digital Library Should Remain Open
On March 30, 2020, the ACM announced that its digital library would be open access for three months. During that time, every conference paper, journal article and book chapter published by the ACM was free to the general public. They didn’t even require a login. The reason to open the digital library was a good one: most people who use it get access through where they work, either in industry or academia. Because of the global pandemic, most people who use it are now working at home, outside of the network which allows them access.
I hoped it would remain open. I shared URLs to papers on the Digital Library on forums, in emails and even in source repos knowing everyone could access the papers at the moment, and hoping that would continue. I even let myself think it was likely that those making the decisions at the ACM would see that this free access had become a public good. I was wrong. On schedule, the ACM Digital Library closed again on June 30, 2020.
It should have remained open. First, because the global pandemic is not over, and few people who read computer science research papers are back at work. Most people who work in the software industry are still at home, and there is still uncertainty about what will happen in American colleges and universities in the next school year.
But more importantly, the ACM Digital Library should have remained open because the most comprehensive repository of computer science research should be freely available to all.
What is the ACM? What is the Digital Library?
The Association for Computing Machinery, or ACM, is a non-profit professional organization for the field of computing. Its stated mission is to support “educators, researchers and professionals” who work in all forms of computing. In practice, I believe the members are primarily computer science educators and researchers and the efforts of the ACM reflect that.
One of the most important functions of the ACM are its conferences and journals. Researchers in academia and industry publish their work through peer-reviewed conference proceedings and journals. For any given field in computer science, there is usually an ACM conference or journal which is one of the top venues to publish in for that field.
The Digital Library is the online repository for all of this research. It has papers published this month all the way back to the beginning of the field of computing in the early 1950s. It is, as far as I know, the most comprehensive single source of computer science research in the world.
What the ACM is not
The ACM is not a for-profit publisher. They are, as said above, a non-profit professional organization. This fact distinguishes them from for-profit publishers like Elsevier. There is a long-standing effort by many in the scientific community to boycott Elsevier and move to open access publications. This boycott has resulted in many organizations ending contracts including Dutch, German and Swedish universities, the University of California system and MIT.
For Elsevier, this fight for open access is existential. They exist to make a profit on scientific publishing. If Elsevier can’t charge for access to the papers it has published, it has no business model and it will cease to exist. The ACM exists to serve the field of computing and society itself. The purpose of the ACM is laid out clearly in Article 2 of its constitution:
The Association is an international scientific and educational organization dedicated to advancing the art, science, engineering, and application of information technology, serving both professional and public interests by fostering the open interchange of information and by promoting the highest professional and ethical standards.
Opening the ACM Digital Library supports every part of that sentence.
My impression is that practitioners are underrepresented in the ACM. These are the professional software developers, product managers and system administrators who do the majority of the professional computing work in our industry. The ACM has on the order of 100,000 members, which is surely a small fraction of the total computing professionals in the world.
When then-president Vint Cerf asked why so many professionals are not members, the closed Digital Library was one of the top answers. Professional organizations exist to serve the profession and the professionals in it—even non-members. The Digital Library should not be a membership perk. It should be the public resource that inspires professionals to become members.
Can’t we get the papers elsewhere?
The moment you write something, you own its copyright. In order for the ACM to publish a paper, we have to transfer copyright. Per that agreement, authors retain the right to publish the paper on their home page (which I do). The institutions the authors work at and the agencies that funded the work are also allowed to publish the paper.
Savvy readers without access to the Digital Library know this fact. Most recent papers can be found by simply Googling its title. Occasionally, finding a free copy of a recent paper requires tracking it down directly from authors’ homepages or institutional publication lists.
If most recent papers are available elsewhere, why all the fuss? There are four reasons:
- Not all recent papers are posted by their authors or institutions. Authors don’t always update their home pages and institutions don’t always post papers. Some authors don’t even have a home page.
- Older papers, from before authors routinely had a home page, are not freely available anywhere.
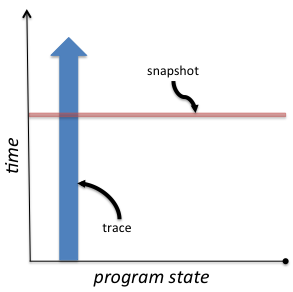
- The Digital Library URL for a paper should be the canonical online home for that paper. If the author does not have a home page or the institution they work for ceases to exist, that URL will always be valid. But people are less likely to share that URL if not everyone can access it. Rather, they will point to the versions scattered throughout the internet.
- The Digital Library itself is valuable: it is a well-designed network of papers, authors, conferences and journals. If you find an interesting paper, you can then easily look at the other papers published in the same conference. Or other papers published by the same author.
I know I’m being unfair
Rationally, three months of open access is better than zero, so the current situation is better than before. Yet, instead of giving the ACM credit for those three months, I’m asking for more. I acknowledge that is unfair. I also acknowledge that the ACM has stated that their eventual goal is general open access. They have several efforts towards this goal: ACM conferences can choose to grant open access to their latest proceedings; authors can pay a fixed fee for their paper to be open; and they established entire journals where all articles must pay the fixed fee to be open.
This is progress, and we must grant credit for incremental improvements. But I fear the ACM is still being too conservative: these efforts are ad-hoc, do not apply to historical papers and do not seem to make open access the primary goal.
I freely admit that I do not know what a sustainable model would look like. But I do know it is possible. While they are smaller in scope, there are major computer science conferences and journals that are completely open access, such as USENIX and VLDB.
I am a member of the ACM, and I intend to be a member for the rest of my life. I criticize it not because it is bad, but because I believe it is good. I just want it to be better.